How to file a police report for identity theft if you discover that you are the victim of identity theft one of the first things you should do is file a report with your local police department many people believe a local police report isn t necessary unless you know the potential perpetrator or believe they're nearby however even if nothing comes from the local police investigation a police report may be required by banks and creditors as proof of your identity when you dispute charges or new accounts reporting identity theft to local police complete an identity theft report with the Federal Trade Commission FTC go to HTTP colon slash slash W W identitytheft.gov or call one eight seven seven four three eight four three three eight to file an identity theft report with the FTC this report will help you organize your information once you complete the report online the FTC will give you a step-by-step recovery plan and checklist based on the information you provided you can prthe report to local police and it will help them with details as they prepare the local police report for you gather documents to support your claim if you have evidence of the identity theft on bank account or credit card statements or on your credit report print these out to prto the police if you receive any email notifications or other information from your bank or credit card company print off copies of those as well you also may have bills or collection notices that include charges you didn't make if you received any email notifications or other information from your bank or credit card company print off copies of those as well you also may have bills or collection notices that include charges you didn't make visit your...
Award-winning PDF software





Identity theft ination Form: What You Should Know
You have a judgment against you for delinquent tax due and overpayment (other information is included). File the Form 14039 (Form 14039F), Statement of Judgment in Payment of Taxes or Statement of Judgment in Payment of Taxes — With Attachment (SJ 1) to any Federal, State, or local tax lien filed against you at any time in the last 15 years. Identity Theft — Alabama Complete IRS Form 14039, Identity Theft Affidavit, if your e-filed return is rejected because of a duplicate filing under your Social Security number (SSN) or you have a judgment against you for delinquent tax due and overpayment (other information is included). File the Form 14039 (Form 14039F), Statement of Judgment in Payment of Taxes or Statement of Judgment in Payment of Taxes — With Attachment (SJ 1) to any Federal, State, or local tax lien filed against you at any time in the last 15 years. Identity Theft — Delaware Fee (and associated paperwork): 100 + 5% of total fee for filing Form 14039; 350 + 10% of total fee for filing Form 14039F; 300 + 10% of total fee for filing Form 14039; (no fee for filing Form 14039F). Identity Theft — Maine If you qualify, complete IRS Form 14039, Identity Theft Affidavit, and, if applicable, attach a copy of your judgment from a judgment creditor or state or local tax lien. Identity Theft — Texas Complete IRS Form 14039, Identity Theft Affidavit, and, if applicable, attach a copy of a judgment (or state or local tax lien) against you for delinquent tax due. Identity Theft — Oregon Complete IRS Form 14039, Identity Theft Affidavit, and, if applicable, attach a copy of a judgment (or a state or local liens against you) or a copy of the tax lien against you and a copy of a judgment against you. Identity Theft — Virginia Complete IRS Form 14039, Identity Theft Affidavit, and, if applicable, attach a copy of a judgment (or a state or local tax lien) against you for delinquent tax due. To learn more about identity theft, and about filing, you should visit IdentityTheft.gov.
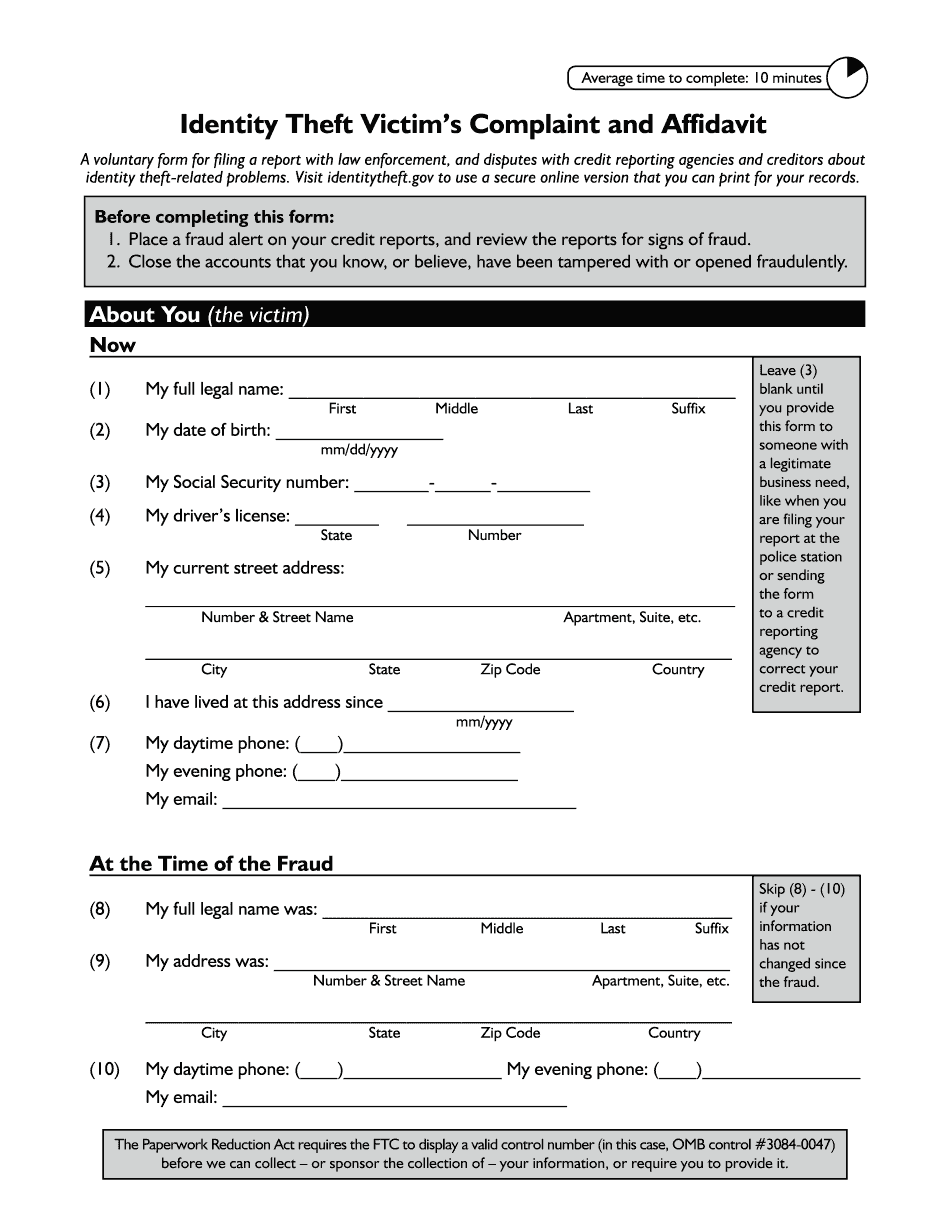
online solutions help you to manage your record administration along with raise the efficiency of the workflows. Stick to the fast guide to do Ftc Identity Theft Victim's Complaint And Affidavit, steer clear of blunders along with furnish it in a timely manner:
How to complete any Ftc Identity Theft Victim's Complaint And Affidavit online: - On the site with all the document, click on Begin immediately along with complete for the editor.
- Use your indications to submit established track record areas.
- Add your own info and speak to data.
- Make sure that you enter correct details and numbers throughout suitable areas.
- Very carefully confirm the content of the form as well as grammar along with punctuational.
- Navigate to Support area when you have questions or perhaps handle our assistance team.
- Place an electronic digital unique in your Ftc Identity Theft Victim's Complaint And Affidavit by using Sign Device.
- After the form is fully gone, media Completed.
- Deliver the particular prepared document by way of electronic mail or facsimile, art print it out or perhaps reduce the gadget.
PDF editor permits you to help make changes to your Ftc Identity Theft Victim's Complaint And Affidavit from the internet connected gadget, personalize it based on your requirements, indicator this in electronic format and also disperse differently.
Video instructions and help with filling out and completing Identity theft information